Organizations are under increasing pressure to modernize infrastructure, improve cyber resilience, simplify operations, and securely support users, applications, and data across distributed environments. At the same time, technology decisions are becoming more interconnected — where networking, security, cloud, identity, governance, and operational visibility must work together as part of a broader architecture rather than as isolated products.
Hararei helps organizations navigate this complexity through practical, architecture-focused solutions spanning Zero Trust security, SASE, SD-WAN, cloud infrastructure, secure remote access, data protection, governance, and operational resilience. Drawing on experience supporting complex enterprise and multinational environments, we work with both technical and business stakeholders to align technology decisions with operational, security, and strategic objectives.
Our approach emphasizes long-term operational outcomes, integration, and scalability — helping organizations modernize securely while reducing complexity and improving visibility across users, applications, and infrastructure.
Hararei are Channel Partners for a range of security products and services

The Secure Application Services Edge (SASE) is the most important development is infrastructure architecture occuring right now. When first defined by Gartner in 2016, the architecture was aspirational, but is now becoming the most important way to deliver applications to users and consumers.
The internet is now the primary network for business applications, user activity, and data exchange. Employees access SaaS platforms, cloud services, and web applications directly from anywhere, often outside traditional network controls. A modern Secure Web Gateway must do more than block threats—it must provide real-time visibility, enforce data protection policies, and control how users interact with the internet across all locations.
Legacy secure web gateways and firewalls were designed for centralized networks, where traffic passed through a data center perimeter. That model no longer exists. Users connect directly to the internet, applications are distributed across cloud platforms, and encrypted traffic dominates.
This creates significant challenges:
Organizations lack visibility into SaaS, AI and web usage, making it difficult to identify risk. Sensitive data can leave the organization without inspection or control. Security policies are inconsistent across office, remote, and mobile users. At the same time, threats have evolved to exploit encrypted channels and cloud services.
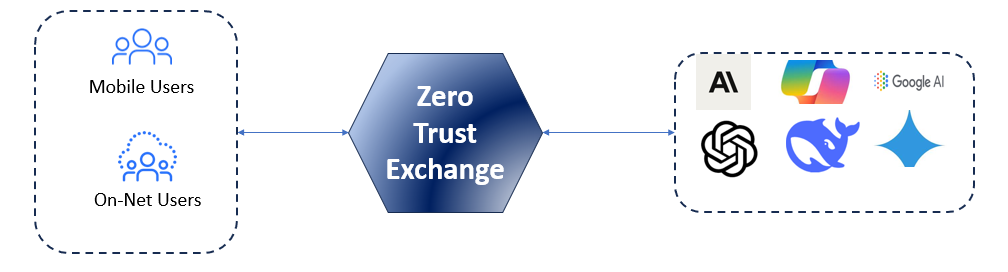
Zscaler Internet Access (ZIA) is the world’s leading Secure Web Gateway (SWG), delivering cloud–native, AI–powered cyberthreat protection to the Internet and SaaS apps. Zscaler’s full proxy architecture enables TLS/SSL inspection at scale, with connections brokered between users and applications based on identity, context, and business policies. ZIA is part of the Zero Trust Exchange (ZTE), and all Internet–bound traffic is be sent through the ZTE.
Zscaler Internet Access (ZIA) Sits inline between your company and the Internet, protecting your enterprise from cyberthreats, stopping intellectual property leaks, and ensuring compliance with corporate content and access policies.
ZIA monitors your network and user activity, secures roaming users and mobile devices, and manages all of this globally from a single management console. There is no hardware to buy, no appliances to manage and policy changes can be effected globally across your organization from a single console in minutes.
Zscaler Internet Access (ZIA) can protect your employees from malware (including Ransomware), viruses and other Internet threats, blocking attacks in real time. Zscaler security services scan and filter every byte of your network traffic, including SSL-encrypted sessions , as it passes to and from the Internet.
Zscaler Internet Security, when combined with ZIA, enables confident, secure AI adoption with a solution that offers AI asset management, secure access to AI, and security for enterprise AI apps and infrastructure, without inhibiting innovation.
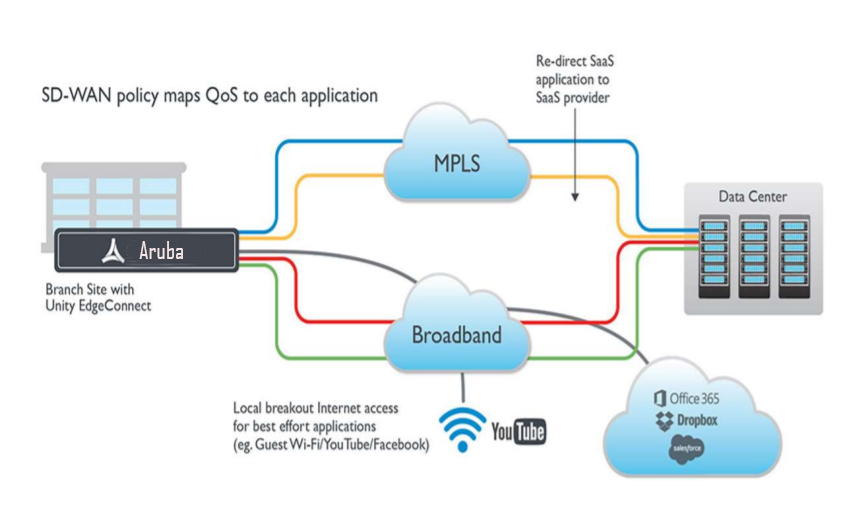
Zscaler Internet Access (ZIA) provides a Secure Service Edge (SSE), which when combined with an SD–WAN product such as Aruba EdgeConnect can provide a complete SASE architecture. It allows secure local breakout for your branch network. SD–WAN makes local breakouts easy. Zscaler makes them secure. Learn more: Network Transformation
One advantage of a cloud–delivered security gateway is that it can be delivered very quickly. See Rapid Internet Protection for a discussion on how protection can be enabled very rapidly. One major airline in the United States, responding to an urgent cyber–event deployed Zscaler to the majority of its users (over 60,000 users) over one weekend, and that included planning time!
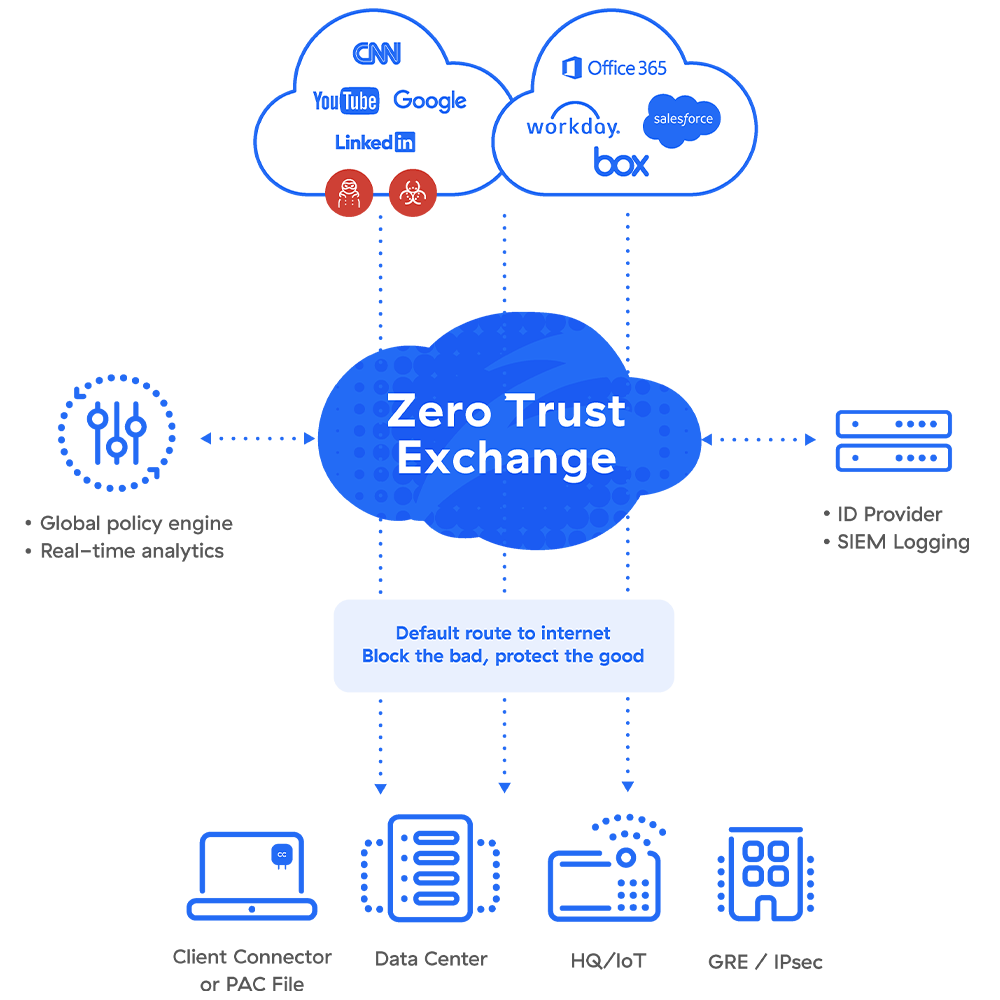
The Zero Trust Exchange (ZTE) is the core component of the Zscaler Secure Web Gateway. All traffic, including encrypted traffic can be routed through the ZTE for inspection and control
Not sure if your current Internet secure web gateway is really secure? Conduct a Security Preview now, from within your existing network to show how effective your current controls are.
The Zscaler Security Preview runs in your
browser. It does not access any data, introduce malware or change
any settings. Click on the button below to begin the Zscaler
Security Preview
Zscaler can also help protect IoT (Internet of Things) and OT (Operational Technology) environments, and help to enable Industry 4.0 in industrial environments. Zscaler can allow for secure data exchange in IoT environments such as Smart City and power generation, and help protect legacy OT environments by providing a Zero Trust Exchange between OT and IT systems.
A modern Secure Web Gateway is a foundational control for managing how users interact with the internet, SaaS applications, and cloud services. As organizations move away from traditional network perimeters, solutions like Zscaler Internet Access provide the visibility, control, and protection required to secure web traffic in real time. The following FAQs address common questions around how a cloud-native SWG works and how it helps organizations reduce risk while enabling secure access from any location.
A Secure Web Gateway is a security control that sits between users and the internet, inspecting and governing web traffic in real time. It is important because most business activity now happens over the internet, including SaaS applications and cloud services. Without a modern SWG, organizations lack visibility into user activity, cannot effectively prevent data loss, and remain exposed to web-based threats.
Zscaler Internet Access is delivered as a cloud-native service rather than an on-premise appliance. Instead of routing traffic through a data center, it inspects traffic inline through a globally distributed platform. This allows organizations to enforce consistent security policies for all users, regardless of location, while eliminating the performance and scalability limitations of traditional gateways.
Zscaler performs full SSL/TLS inspection at scale, allowing organizations to identify threats and enforce policies within encrypted traffic. Since the majority of internet traffic is now encrypted, this capability is essential for detecting malware, preventing data leakage, and maintaining visibility into user activity.
Zscaler includes integrated Data Loss Prevention capabilities that inspect outbound traffic in real time. It can detect sensitive information such as personal data, financial records, or intellectual property and apply policies to block, allow, or log the activity. This ensures that data is protected as users interact with web and SaaS applications.
Zscaler provides detailed visibility into all web and SaaS applications being accessed by users. It can identify unsanctioned or risky applications and allow organizations to apply policies that restrict or control their use. This helps reduce risk associated with shadow IT while enabling safe adoption of cloud services.
Zscaler is designed to improve user experience by routing traffic directly to the nearest point of presence rather than backhauling it through a central data center. This reduces latency and improves application performance, particularly for cloud and SaaS applications, while still enforcing full security inspection.
Zscaler uses a combination of real-time inspection, threat intelligence, and advanced detection techniques to identify and block malicious content before it reaches the user. By inspecting traffic inline and enforcing policy before connections are established, it reduces the attack surface and prevents threats from entering the environment.
Because Zscaler operates in the cloud, it applies the same security policies to users regardless of where they are located. Whether users are in an office, at home, or traveling, their internet traffic is routed through the Zscaler platform, ensuring consistent protection without relying on VPNs or on-premise infrastructure.
Zscaler provides centralized logging and reporting across all internet activity, allowing organizations to demonstrate how policies are enforced and how data is protected. Security and compliance teams can generate reports that show user activity, application usage, and policy enforcement, making it easier to meet regulatory requirements and internal governance standards.
Selecting a secure web gateway is not just a product decision — it is an architectural one.
At Hararei, we help organizations evaluate how secure web gateway capabilities fit into a broader strategy that includes SASE, Zero Trust, and cloud transformation. With extensive experience deploying Zscaler across diverse environments, we ensure that the solution is aligned to business objectives, cost and performance requirements, and regulatory needs. Our management have decades of experience managing secure, regulated environments and can assist in ensuring the technologies we represent can meet your regulatory requirements.
ZTNA, or Zero Trust Network Access, provides secure, identity-based access to private applications and data for users and devices by verifying their identity and device health before granting temporary, granular access to only the necessary resources, rather than broad network access. It replaces traditional VPNs by creating a "software-defined perimeter" (SDP) for each user and application, significantly reducing the attack surface and improving security for modern, cloud-first organizations.
Zscaler Private Access (ZPA) is a next-generation, non-VPN based solution for secure remote access. The patented Zscaler Private Access solution works by abstracting the private, internal application from the network on which it resides, providing access from authorized users to specific applications via encrypted, per–session microtunnels that are created upon demand.
The end user is never directly connected to the application, nor is the user connected to the network on which the application resides. ZPA instead delivers functionality similar to a forward and a reverse proxy acting together. This ensure that networks and applications cannot be infected or exploited by open network tunnels.
Zscaler is a platform, which means Zero Trust can be combined with other security functions such as Data Loss Prevention, Cloud Application Access, Application Bandwidth Management, and Secure Web Gateway in a single platform. This platform can then be used for management and complicance reporting and security monitoring. For an example of a holistic platform approach to application, see our Zscaler for SAP page.
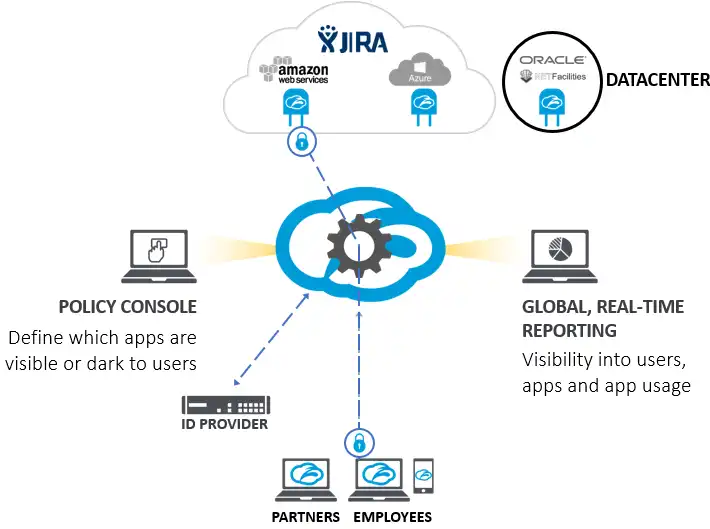
Zero Trust Network Access is one component of a Secure Access Service Edge (SASE) architecture.
Learn more at: Zero Trust Network Access
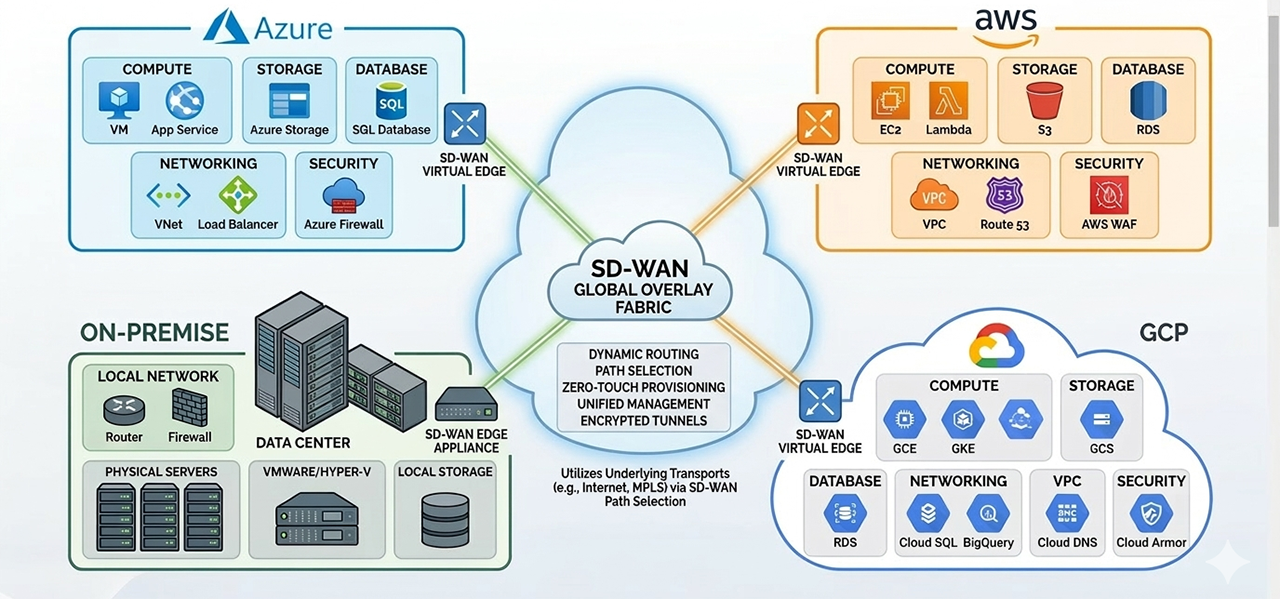
Modern enterprises depend on applications delivered from private data centres, public cloud platforms, SaaS providers, and increasingly multiple cloud environments. Traditional WAN architectures were not designed for this level of distribution and often result in higher costs, inconsistent performance, and increased operational complexity. Advanced SD-WAN provides an intelligent software-defined fabric that continuously optimises connectivity, improves application performance, reduces dependency on expensive MPLS circuits, and establishes a strong foundation for Secure Access Service Edge (SASE).
Traditional hub-and-spoke WAN architectures were designed for a world where applications lived in central data centres. That world no longer exists. Today, enterprise applications run across AWS, Azure, SaaS platforms, and distributed data centres. Backhauling every packet through a central location — over expensive MPLS circuits — introduces latency, inflates costs, and degrades the user experience for remote and branch workers. The result is a network that works against your business rather than for it:
A new architecture is required — one that puts application performance and security at the centre of WAN design.
Advanced SD-WAN solves the cloud connectivity problem by intelligently routing traffic across multiple network transports — MPLS, broadband, 5G, or any combination — while maintaining strong security controls and consistent application performance.
Unlike basic SD-WAN products that simply load-balance across links, an advanced SD-WAN platform continuously monitors latency, packet loss, and jitter on every available path and steers each application's traffic in real time to the optimal route. Business-critical applications always get priority. Best-effort traffic takes whatever path is available.
The four business outcomes that advanced SD-WAN delivers:
Integrated next-generation firewall with IDS/IPS and role-based segmentation enforces Zero Trust security policies at every branch edge — eliminating the need for standalone branch firewalls and reducing hardware footprint.
Direct, policy-driven connectivity to AWS, Azure, and leading SaaS providers — without backhauling cloud-destined traffic through a central data centre. First-packet application identification ensures traffic takes the optimal path from the moment a session begins.
Dynamic path selection, packet loss mitigation, TCP optimisation, and data deduplication keep business applications responsive even over broadband and internet circuits. Voice, video, and latency-sensitive applications perform as reliably as they would on a private network.
Supplement or replace expensive MPLS circuits with broadband and internet connectivity. Centralised orchestration and zero-touch provisioning also reduce the time and resources required to provision and manage branch networks — lowering both capital and operational expenditure.
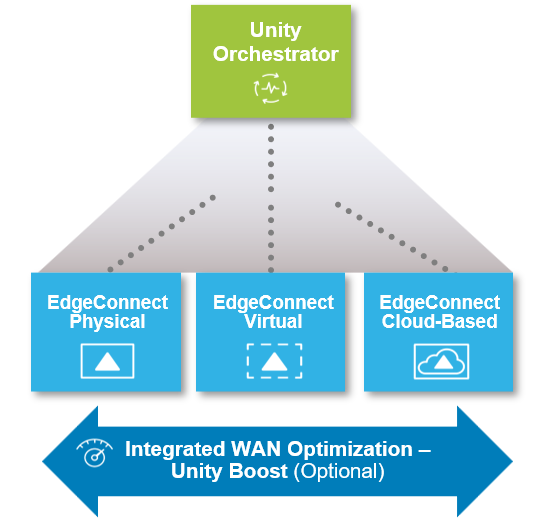
HPE Aruba EdgeConnect is the advanced SD-WAN platform Hararei has deployed across enterprise networks in India, the UAE, and the United States. It is purpose-built to deliver secure, high-performance connectivity across branch offices, data centres, and cloud environments.
EdgeConnect creates encrypted virtual network overlays across any available transport, connecting users directly to applications while maintaining consistent security policies and predictable performance — regardless of the underlying network.
Key platform capabilities:
Advanced SD-WAN platforms deliver consistent application performance across any network transport by intelligently monitoring and steering traffic based on real-time network conditions. Capabilities such as dynamic path selection, packet loss mitigation, TCP optimization, and data deduplication allow organizations to maintain reliable performance even when using broadband and internet circuits. By continuously adapting to changing network conditions, advanced SD-WAN ensures that business-critical applications remain responsive whether they are delivered from data centers, cloud platforms, or distributed enterprise environments.
HPE Aruba EdgeConnect is an advanced SD-WAN platform designed to provide secure, high-performance connectivity across branch offices, data centers, and cloud environments. By creating encrypted virtual network overlays across any available transport, EdgeConnect enables organizations to connect users directly to applications while maintaining consistent security policies and predictable application performance.
EdgeConnect continuously monitors network conditions including latency, packet loss, and jitter, and dynamically steers traffic across the optimal path in real time. Integrated WAN optimization technologies such as packet conditioning, TCP acceleration, and data deduplication further improve application responsiveness across long-distance or high-latency connections.
With centralized orchestration and zero-touch deployment capabilities, Aruba EdgeConnect simplifies network operations while allowing organizations to augment or replace traditional MPLS circuits with broadband and public internet connectivity. The result is a flexible, cost-effective WAN architecture that supports modern multi-cloud application environments.
Identifies business applications and applies policies based on performance, priority, and business importance.
Continuously measures latency, jitter, and packet loss and selects the optimal path in real time.
Uses forward error correction and packet duplication to improve voice, video, and critical application performance.
Reduces bandwidth consumption through compression, caching, and data deduplication.
Provides policy-based management and visibility across all branches from a single console.
Creates a high-performance underlay for Security Service Edge and Zero Trust architectures.
Secure, Encrypted SD-WAN: With increased snooping on networks, insecure default hardware configurations, and an uncertain chain of custody for international networks, what can an enterprise do to ensure their private data stays private? Learn how Hararei can help to secure your WAN traffic: Secure Overlay Network.
Thin Branch:A significant source of ongoing operational costs for widely distributed enterprises is the expense associated with running branch operations. Whether it is bank branches, retail stores, government offices or insurance agencies, the costs associated with the branch network are a significant portion of the cost structure of the distributed enterprise. A Thin Branch solution will help reduce these operational costs
Multi-Cloud networking: Native cloud interconnects and point-to-point VPNs are expensive, operationally complex, and difficult to scale. They lack intelligent traffic management, leave security policy fragmented, and can't adapt dynamically to changing application demands. The result is higher costs, degraded performance, and a growing attack surface. Multi-Cloud Networking can resolve these issues.
Enterprise network architectures were designed for a world where applications lived in centralized data centers and users worked from corporate offices. Today, applications are distributed across SaaS platforms, public clouds, and regional data centers, while employees, partners, and contractors access these systems from virtually anywhere. At the same time, organizations must defend against increasingly sophisticated cyber threats while supporting bandwidth-intensive applications and a growing number of connected devices.
Traditional WAN and security architectures struggle to keep pace with these changes. Backhauling traffic through centralized data centers introduces latency, increases cost, and creates operational complexity, while fragmented security tools make it difficult to enforce consistent policies or maintain visibility across the environment. As a result, many organizations are reevaluating how networking and security should be delivered in a cloud-first world.
By modernizing both WAN and security architectures through SASE, organizations can enable direct, secure access to applications and services across on-premise infrastructure, public cloud environments, and SaaS platforms—regardless of where users or devices are located.
At Hararei, we understand that adopting a modern infrastructure architecture is a strategic journey. Our team helps organizations plan, implement, and operate these cloud-generation networking and security technologies with a structured and pragmatic approach.
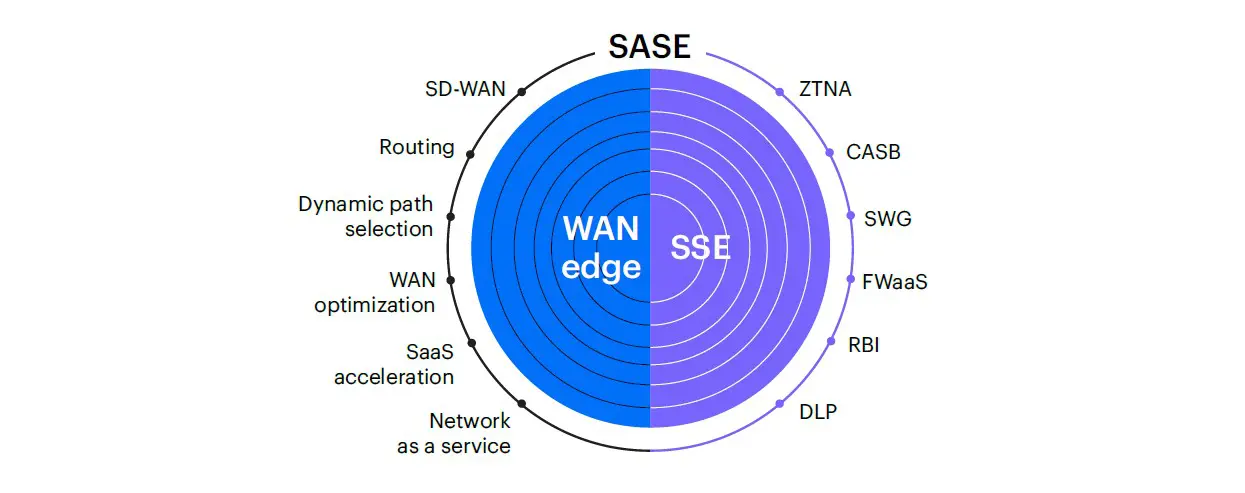
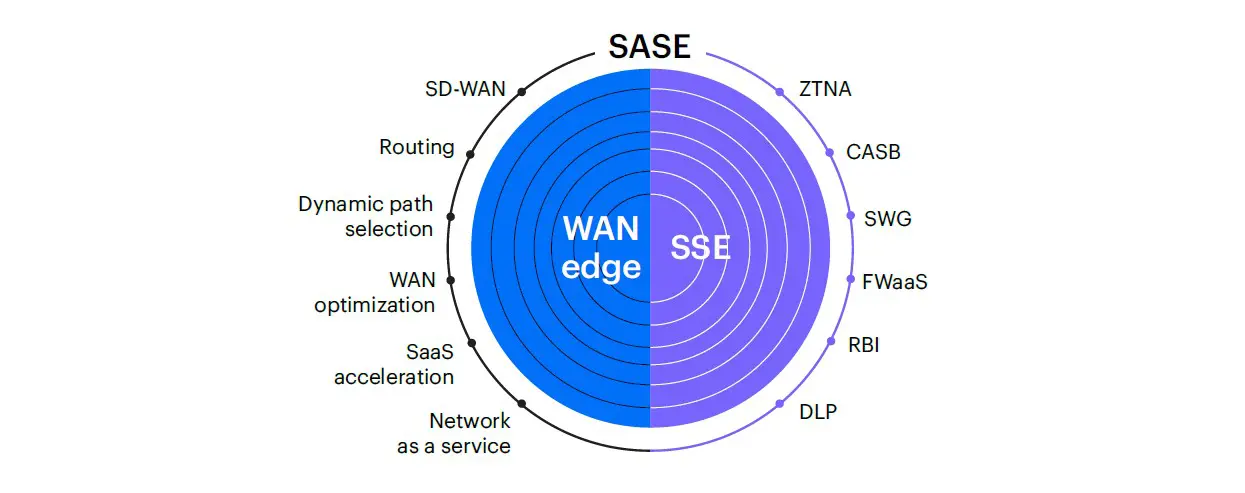
Secure Access Service Edge (SASE) combines an advanced SD-WAN edge deployed at branch locations with a comprehensive, cloud-delivered Security Service Edge (SSE) platform that provides integrated networking and security capabilities.
There is no universally correct answer. The right SASE architecture depends on your organization's priorities, existing environment, and operational model. That said, there are clear indicators that point toward one approach over the other.
Single-vendor SASE tends to be the better fit when:
Best-of-breed tends to make more sense when:
For a detailed look at the technical capabilities of the HPE Aruba Networking unified SASE platform, download the overview brochure.
Our position. We work with both architectures and have no preference other than what's right for your situation. If a single-vendor approach fits, Aruba's platform is one of the most capable available. If best-of-breed is the better answer, we can design and implement that too.
A single-vendor SASE solution combines SD-WAN and Security Service Edge (SSE) capabilities within a unified platform — managed through a single console, governed by a single policy engine, and supported by a single vendor relationship.
The practical benefits of this approach are significant:
Single-vendor SASE is particularly well suited to organizations that are modernizing their WAN and security architectures simultaneously, want to reduce operational complexity, or are moving away from a fragmented set of point solutions toward a more unified infrastructure model.
Aruba's SASE platform brings together SD-WAN and Security Service Edge capabilities in a unified architecture, managed through a single cloud-based console
Aruba EdgeConnect is the WAN edge component, deployed at branch locations and data centers. It provides application-aware routing, WAN optimization, and traffic steering across multiple underlay transports *mdash; broadband, LTE, MPLS — with automatic failover and path selection based on real-time link quality. EdgeConnect replaces traditional branch routers and WAN appliances while delivering significantly better application performance and visibility.
The SSE component delivers cloud-based security services that protect users and devices regardless of where they connect from:
Both the SD-WAN and SSE functions are managed throughone portal, providing a single view of network performance, security events, and policy across the entire environment. This eliminates the operational overhead of maintaining separate management planes for networking and security.
Deploying SASE is not a product purchase — it's an architectural shift that touches networking, security, identity, and operations simultaneously. Getting it right requires more than just technical capability; it requires a structured approach and experience across a wide range of enterprise environments. Hararei has been designing and deploying SASE architectures for more than eight years. We bring that experience to every engagement through a consistent, pragmatic delivery model:
Every organization's path to a modern network and security architecture is different. Whether you are at the early stages of evaluating options, working through a business case, or ready to begin a deployment, we are happy to have a straightforward conversation about your requirements and what an appropriate architecture might look like.
There is no obligation and no sales pitch — just an honest discussion about whether SASE makes sense for your situation, and if so, how to approach it.
Most enterprises today don't live in a single cloud. Workloads are spread across Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP) — driven by best-of-breed services, data sovereignty, regulatory requirements, mergers, or simply the pace of digital transformation. But while multi-cloud delivers flexibility, it introduces a critical challenge: How do you connect these environments securely, reliably, and cost-effectively?
Native cloud interconnects and point-to-point VPNs are expensive, operationally complex, and difficult to scale. They lack intelligent traffic management, leave security policy fragmented, and can't adapt dynamically to changing application demands. The result is higher costs, degraded performance, and a growing attack surface.
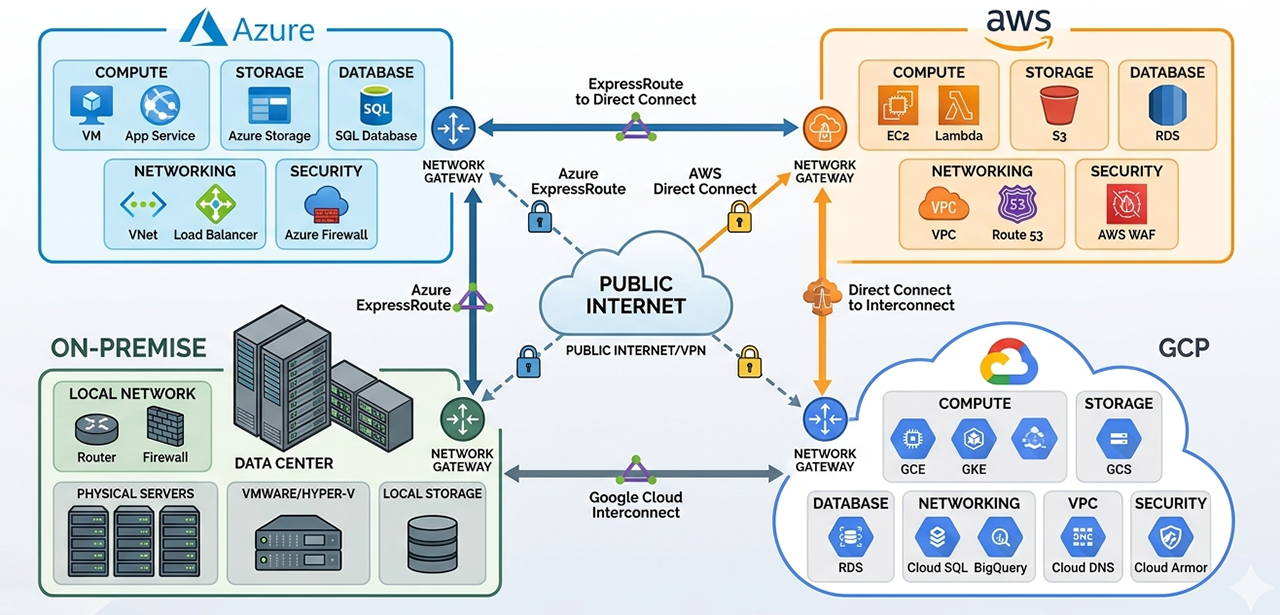
Traditional approaches to connecting cloud environments — static VPNs, expensive MPLS extensions, and manual peering — cannot meet the demands of modern, distributed enterprises. Organizations need a smarter, unified fabric that spans all major cloud providers without sacrificing security or performance.
Hararei brings over 8 years of SASE and SD-WAN deployment experience to solve multi-cloud networking. Leveraging HPE Aruba EdgeConnect — one of the industry's most advanced SASE/SD-WAN platforms — Hararei delivers a secure, automated, and intelligent networking fabric that spans AWS, Azure, GCP and on-premise environments simultaneously.
EdgeConnect's virtual overlay technology abstracts the underlying transport — whether that's internet broadband, cloud provider interconnects, 4G/5G mobile or private circuits — and creates a unified, policy-driven network across all cloud environments.
With real-time insight into network and application health, AI-driven network adaptation and automated fault isolation, users will experience the perfect WAN!. Advanced SD-WAN features can perform packet-by-packet routing to address underlying network brownouts, and TCP mitigation to address high-latency network issues
Hararei designs inter-cloud SD-WAN architectures tailored to each customer's environment. The following illustrates a typical multi-cloud deployment:
Environment |
Architectural Elements |
|---|---|
AWS (Primary) |
EdgeConnect virtual appliance deployed in AWS VPC.Direct Connect or broadband overlay to Azure, GCP or On-premise environments. Integrates with AWS Transit Gateway to support complex VPC configurations. |
Microsoft Azure |
EdgeConnect deployed in Azure VNet. Integrated with Azure Virtual WAN or standalone hub model. Policy-consistent with AWS environment. |
Google Cloud Platform |
EdgeConnect deployed in GCP VPC. Supports Cloud Interconnect augmentation or pure internet overlay. Full mesh or hub-and-spoke topology options. |
On-Premise Environments |
EdgeConnect deployed in customer environment, Supports virtual or physical appliances. Full mesh or hub-and-spoke topology options. High-availability (HA) options. |
Security Integration |
Integration with SD-WAN and SSE environments. Local breakout via SD-WAN to trusted applications, direct egress to SSE (e.g. Zscaler) for traffic inspection. Options for on-board SSE with Aruba EdgeConnect. Ingress using ZTNA. |
Management |
Full connectivity management including routing, traffic optimisation and real-time congestion management using SD-WAN features through a single management application (better than single pane-of-glass with multiple windows) |
Hararei's multi-cloud networking solution delivers measurable outcomes across cost, performance, and risk dimensions — the three things every technology leader is ultimately accountable for.
Cost Reduction |
Replace expensive dedicated cloud interconnects and MPLS links with broadband overlays. Aruba EdgeConnect customers have reported WAN cost reductions exceeding 90% in some cases. |
Performance |
Intelligent path selection ensures applications always use the optimal route. Consistent, low-latency connectivity between cloud environments regardless of traffic conditions. |
Security Posture |
Private traffic is encrypted between sites with end-to-end encryption, preventing snooping even by telecom intermediaries. Private traffic is never exposed to the Internet. Ingress/Egress traffic can be integrated with any SSE solution. |
Operational Simplicity |
Centralised management via Aruba Orchestrator eliminates per-cloud, per-region configuration complexity. Policy changes propagate globally in minutes. Complex policy changes due to changing business requirements can be implemented immediately instead of needing to reconfigure low-level routers individually. |
Agility |
Spin up new cloud regions or migrate workloads between clouds without re-architecting the network. The SD-WAN fabric can adapt automatically. |
Risk Reduction |
Consistent security policy across all cloud environments reduces the attack surface and supports compliance with frameworks such as ISO 27001, SOC 2, and GDPR. Detailed fabric-wide reporting provides comprehensive visibility for administrative or regulatory reporting |
Hararei is not just a reseller — we are a trusted IT advisor with deep, certified expertise in SD-WAN, SASE, and cloud architecture. Our team has delivered complex, large-scale network transformations for enterprises across financial services, healthcare, retail, and manufacturing, with deployments spanning Wall Street, the City of London, Hong Kong, Singapore, Tokyo, and Mumbai.
Every Hararei engagement includes ongoing Level 4 strategic support: architecture reviews, configuration recommendations, new product updates, and MIS reporting. We stay engaged to ensure you get maximum value from your investment — at no additional charge.
Every multi-cloud networking journey is unique. Hararei offers a complimentary Multi-Cloud Networking Assessment that evaluates your current environment and delivers a tailored roadmap. The assessment covers:
The assessment is conducted by Hararei's senior architects and is provided as part of our Trusted IT Advisor commitment — at no cost to you.
Contact the Hararei team today to schedule your complimentary Inter-Cloud Networking Assessment. Our experts will help you design a secure, high-performance, and cost-effective multi-cloud fabric tailored to your organisation.
Zscaler is a cloud-delivered security platform that extends Zero Trust protection to IoT and OT environments. While many OT systems have historically remained isolated for security reasons, this limits the ability to adopt Industry 4.0 initiatives such as real-time analytics, automation, and remote operations.
All your IoT/OT devices would essentially sit behind Zscaler's Zero Trust Exchange, so you can protect industrial control systems, SCADA systems, factory and manufacturing lines and other critical assets. Zscaler ensures these devices remain secure and compliant, minimizing downtime, attacks and data loss
The Zscaler platform leverages a global Cloud that runs at the edge of your devices for lightweight, fast connections which can scale much faster than any other IoT/OT secure access solution on the market.

Zscaler can help secure OT (Operational Technology) environments by providing a comprehensive security platform that can detect and prevent cyber threats before they reach the OT environment. Zscaler's cloud-based security architecture provides a secure and direct access to the Internet, eliminating the need for backhauling traffic through legacy security devices or appliances. It provided a single pane of glass to manage security across all locations, device and users, and enables seamless security operations.
Zscaler's zero-trust security model ensures that only authorized devices and users can connect to the OT network, reducing the attack surface and preventing unauthorized access. It can also help secure IoT devices and other OT assets, ensuring they are compliant with industry standards and regulations.
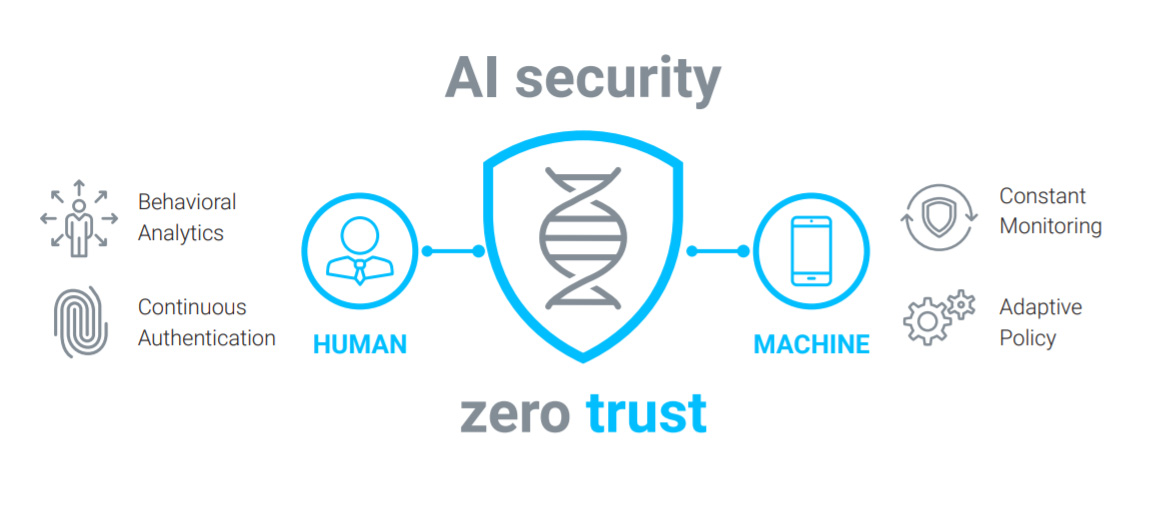
A zero trust approach is the most effective way to ensure robust ICS and OT security and achieve IEC 62443 compliance with adaptive, context-based application access that doesn’t depend on network access. With an effective zero trust architecture in place, any user can only access the applications and systems they need, with no complex firewall stacks or VPNs required, all while your apps and network stay invisible to the internet.
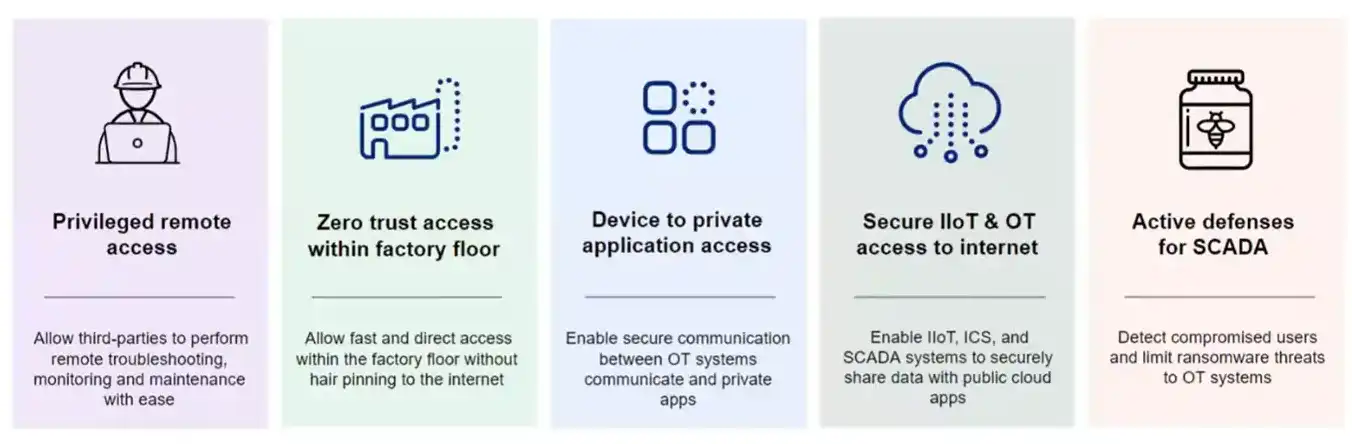
Zscaler solves IIoT and OT use cases by routing traffic through the Zscaler Zero Trust Exchange (ZTE). This solves for at least 5 differennt Use Cases
Modern manufacturing, logistics, healthcare, and critical infrastructure environments depend on the secure integration of operational technology (OT) and IoT devices with enterprise IT systems. However, these devices are often unmanaged, unpatchable, and inherently vulnerable. Bridging OT and IT without proper segmentation and inspection dramatically increases risk and expands the attack surface. A security-first architecture enables controlled connectivity, granular policy enforcement, and continuous visibility across all devices—allowing organizations to unlock real-time analytics, automation, predictive maintenance, and digital transformation initiatives without compromising safety or resilience.
From a technical standpoint, secure OT and IoT integration requires identity-aware segmentation, full traffic inspection, and policy enforcement independent of network location. Rather than relying on flat VLAN designs or perimeter firewalls, modern architectures apply zero trust principles to device communications—validating device identity, restricting east-west movement, and limiting access strictly to required applications and services. Continuous monitoring, encrypted DNS, and granular policy controls ensure that unmanaged or legacy devices cannot laterally propagate threats. This approach reduces blast radius, strengthens compliance, and provides the operational visibility required to safely scale connected environments.
From a financial perspective, securely integrating OT and IoT environments protects far more than data — it protects uptime, production capacity, and revenue. Unsegmented device networks increase the likelihood of operational disruption, regulatory penalties, and costly incident response. By enforcing granular segmentation and centralized policy control, organizations reduce the probability and impact of outages while lowering the long-term cost of managing fragmented security tools. A platform-based security architecture also simplifies operations, reduces vendor sprawl, and improves predictability of total cost of ownership, allowing Industry 4.0 initiatives to scale without introducing uncontrolled financial risk.
A zero trust approach is the most effective way to ensure robust OT security. With an effective zero trust architecture in place, any user—an employee, a contractor, or a third party—can only access the applications and systems they need to do their job, with no complex firewall stacks or VPNs required, all while your apps and network stay invisible to the open internet.
Hararei is a Cloud Generation solutions provider committed to helping clients prepare for, adopt and deploy the latest generation of applications, cybersecurity solutions and IT/Cloud infrastructure. Contact us today for a confidential discussion regarding all your Cloud and Edge requirements, including how to deploy Zero Trust in any environment.
The Cloud service model has evolved to the point where IT and business leaders usually ask why applications cannot be delivered on the Cloud. Whether the model is public or private, IaaS, PaaS or SaaS, it is usually cloud first. Cloud can be an integral part of any operating environment whether it is the primary hosting environment or a component in a data protection strategy.
Managing on-premises infrastructure is increasingly expensive and difficult to scale. Hardware refreshes, capacity planning, disaster recovery, and security patching all consume time and budget that could be spent on the business. And the gap keeps widening — cloud providers like AWS invest billions annually in infrastructure, security, and innovation at a pace that all but the largest enterprises simply cannot match on their own. But migrating to the cloud introduces its own complexity — choosing the right services, managing costs, meeting compliance requirements, and avoiding disruption during the transition.
Hararei is an AWS Consulting Partner specializing in cloud IaaS, migration, and disaster recovery. We work across the full AWS stack, so whether it's a single workload or a full enterprise migration, we help you plan and execute each phase.
More and more companies are embracing the Public Cloud for IaaS/PaaS.
Cloud migrations can range from simple provisioning of a couple of AWS virtual servers, to entire applications with stringent data protection requirements, or to entire enterprises with complicated global privacy and regulatory requirements. Consider the following solutions for your Cloud Journey:
Leveraging AWS best practices, Hararei partners with you to define a multi–phased roadmap for your Cloud Journey:

We talk about our cloud philosophy in our Cloud First blog post.
Remember, at the end of the day, every CEO only cares about three things:
IT started to embrace public SaaS years ago (SalesForce, WebEx, HR/Payroll services, etc.). And now, more and more companies are leveraging IaaS and PaaS in the public cloud too. Why? Simple - their IT leaders realized that the benefits associated with public cloud (time to market, speed, agility, no CapEx, low OpEx, feature rich, flexibility, scalability, elasticity, security, etc.) will help to achieve some if not all of things CEOs care about.
Hararei provides a range of cloud-based Disaster Recovery solutions to suit every budget and recovery objective. From simple Backup/Restore solutions to full-scale Active/Active solutions that operate across multiple sites or Clouds, Hararei can help you implement a Disaster Recovery solution that meets your requirements.
Hararei is an AWS Consulting Partner and has the commercial IT experience to properly architect and implement a robust Disaster Recovery strategy
Many companies provide a Disaster Recovery environment to ensure continued operation during natural disasters, political strife, epidemics or other potential disruptions to business. The IT Disaster Recovery Plan is typically part of a wider Business Continuity Programme, and it can be a major expense for any company.
Expenses involved in providing a Disaster Recovery capability can often approach (or even exceed, due to data replication requirements) the cost of the primary IT Production costs, which leads some comapnies to try to save money by reducing the capabilities in the Disaster Recovery environment.
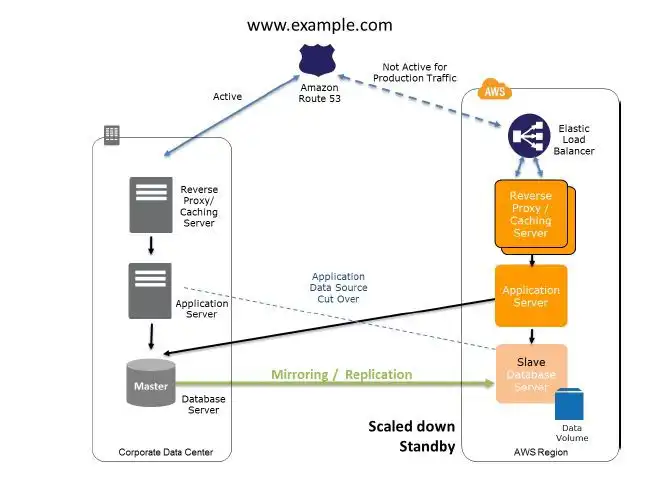
The good news is that Amazon Web Services (AWS) can be used as part of a strategic IT Disaster Recovery Plan and will usually be lower in cost than existing capabilities, and most likely provide a better time to recovery. We outline 4 different strategies here that can form the basis of an effecient and cost-effective Disaster Recovery plan:
The actual strategies used depends on recovery time and recovery point (RTO/RPO) requirements and budgets, and will be different for every company.
MSP360 provides software for backups to the Cloud with limitless point in time restore capabilities, ensuring that even if you are hit with a ransomware attack, you can roll back your user devices to a point prior to the attack
MSP360™ (formerly CloudBerry Lab) is an easy-to-use cloud backup management solution with military-grade encryption.
Customers can choose to provision their own storage using any of the major cloud storage providers including AWS, Microsoft Azure, Google Cloud, Wasabi and others, or Hararei as an AWS Partner can provide AWS storage. Unlike other solutions, the customer is NOT locked into a storage provider.
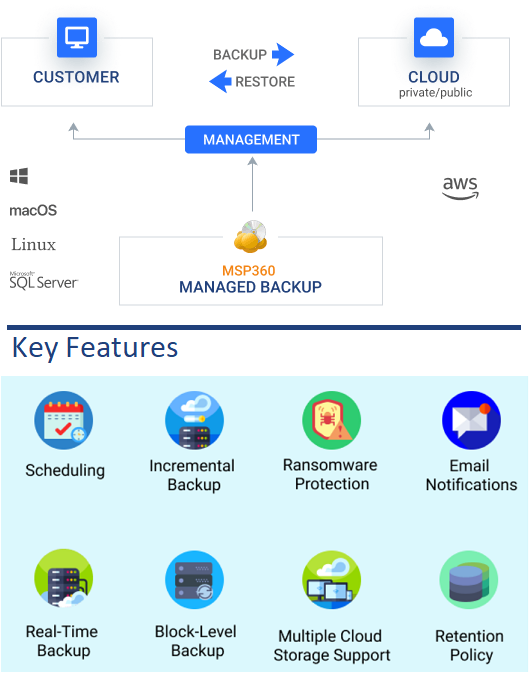
Key features include:
Security Management remains a critical function for IT departments regardless of where applications are hosted or what the connectivity looks like. Protecting the organization from endpoint to data center requires a holistic approach that crosses multiple technical domains.
Generative AI is moving into the enterprise faster than most security and governance frameworks can keep up. Employees are already using AI tools across the business — often over encrypted traffic and outside traditional security controls.
AI can drive productivity, speed decision-making, and improve customer experiences. It can also create a new class of security and compliance risk.
Drawing on real-world experience in highly regulated environments—including financial services, capital markets, and global payroll systems—Hararei can help organizations safely adopt AI by combining Zscaler's cloud-delivered security with practical, policy-driven governance.
In practice, most organizations already have AI usage happening today—they just don’t have visibility or control over it.
Without the right controls, organizations may be unable to reliably:
Blocking AI entirely is not the answer. The goal is to enable AI securely—with visibility, governance, and real-time control.
Zscaler Inspects All Traffic Going To The Internet, Including AI Applications
AI applications can be identified and categorized across the organization, including generative AI platforms, coding assistants, browser extensions, and AI-enabled SaaS services. This enables security teams to detect shadow AI, understand usage trends, and make informed policy decisions.
Inline inspection of web and SaaS traffic helps prevent sensitive data from being submitted to AI engines to prevent sensitive data from being submitted. DLP policies can be used to block or alert on customer information, financial data, intellectual property, and regulated information before it leaves the organization.
Organizations can control not only which AI services employees may access, but also how those services are used. Policies can allow approved AI tools, block unsanctioned or high-risk services, and restrict access by role, department, or device posture. Session controls can also limit actions such as uploads, copy/paste, and other risky interactions.
Most AI applications operate over encrypted HTTPS. Zscaler decrypts and inspects traffic inline, enabling organizations to inspect prompts, enforce policy, and detect sensitive data exposure in ways that traditional perimeter tools cannot.
Through inline CASB and browser isolation capabilities, Zscaler can enforce granular controls over user interactions within AI and cloud applications. These controls can block copy/paste into prompts, restrict file uploads, prevent downloads of AI-generated files, isolate unsanctioned applications, and enforce restricted sessions for unmanaged devices.
Zscaler Gen AI protection extends beyond app access by inspecting both prompts and responses in real time. It adds AI-specific protections such as prompt inspection, DLP for AI interactions, detection of prompt injection and jailbreak attempts, and content moderation for unsafe or non-compliant output.
These risks are not theoretical. In real environments, organizations are already seeing sensitive data shared with AI platforms, often without malicious intent—simply due to lack of visibility and control.
With Zscaler, organizations can move from unmanaged AI adoption to policy-driven AI enablement by:
Data protection regulations require organizations to control how sensitive data is used and shared. Generative AI introduces a new risk — employees can unknowingly submit regulated or confidential data into external AI platforms, often without visibility.
Zscaler helps address this by inspecting prompts, enforcing data protection policies, and restricting AI usage to approved workflows — ensuring AI adoption aligns with security and compliance requirements.
Hararei brings practical, real-world experience securing sensitive data in complex, regulated environments—including financial services, capital markets, and global enterprise platforms.
We understand that securing AI is not just a technology problem—it is a policy, governance, and operational challenge. Our approach focuses on aligning Zscaler capabilities with how organizations actually use data, applications, and AI in production environments.
From initial visibility into AI usage, to defining enforceable policies, to implementing controls without disrupting the business, Hararei helps organizations move from theoretical AI risk to practical, secure AI enablement.
Achieving next-generation, AI-enhanced protection by leveraging Zscaler's platform with the expertise of Hararei.
Zscaler helps organizations address key risks associated with AI usage, including the unintended exposure of sensitive data through prompts, the use of unsanctioned AI applications, and interactions with potentially harmful or manipulated AI content. By inspecting traffic inline through the Zero Trust Exchange, Zscaler ensures that policies are enforced before data is transmitted to external AI platforms, reducing the likelihood of data leakage or misuse.
Zscaler uses integrated Data Loss Prevention capabilities within Zscaler Internet Access to inspect user interactions with AI platforms in real time. When a user submits a prompt or uploads data, Zscaler analyzes the content for sensitive information such as personal data, financial records, or intellectual property. Based on defined policies, it can block the request, allow it with modifications, or log the activity for further review, ensuring that sensitive data is not inadvertently exposed.
Zscaler provides full visibility and control over AI application usage through its cloud access security broker functionality. It can identify AI applications being accessed across the organization and distinguish between sanctioned and unsanctioned tools. Policies can then be applied to allow access, restrict usage, or completely block certain applications, helping organizations prevent uncontrolled or risky adoption of AI services.
Zscaler reduces exposure to prompt injection and malicious outputs by inspecting outbound requests and applying security policies that identify suspicious or high-risk interactions. In addition, it can leverage browser isolation to ensure that responses from AI platforms are executed in a controlled environment. This approach limits the potential impact of malicious content without requiring changes to the underlying AI models themselves.
Zscaler provides detailed visibility into user activity across AI platforms, allowing organizations to understand how these tools are being used in practice. This includes tracking which applications are accessed, how frequently they are used, and, depending on policy configuration, the nature of the interactions. This level of insight enables security and compliance teams to assess risk and refine governance strategies around AI adoption.
Because Zscaler operates as a cloud-native platform, it applies consistent security policies regardless of where users are located. All traffic is routed through the Zero Trust Exchange, whether users are on a corporate network, at home, or traveling. This ensures that interactions with AI services are always subject to the same inspection and control mechanisms, eliminating gaps that might otherwise arise in remote or hybrid work environments.
Zscaler can isolate AI sessions using its browser isolation capabilities, which execute web sessions in a secure, remote environment rather than on the user’s device. This allows organizations to tightly control how users interact with AI tools by restricting actions such as copying, pasting, downloading, or uploading data. As a result, sensitive information is prevented from being exposed either to the AI service or to the endpoint.
Zscaler supports compliance efforts by enforcing data protection policies on all interactions with AI services and maintaining detailed audit logs of user activity. Organizations can define how data is handled, ensure that sensitive information is not transmitted to external platforms, and demonstrate adherence to regulatory requirements through reporting and monitoring capabilities. This enables safe and governed adoption of AI within regulated environments.
Zscaler simplifies reporting and compliance by providing centralized, easy-to-consume visibility into all user interactions with AI applications. Through integrated logging and analytics across the Zero Trust Exchange, organizations can quickly generate reports that show who is using AI tools, what data is being shared, and whether policies are being enforced. This allows security, risk, and compliance teams to demonstrate adherence to internal policies and external regulations without relying on multiple tools or manual data collection, significantly reducing the operational burden of governing AI usage.
Speak with Hararei to understand how Zscaler can help your organization gain visibility into AI usage, prevent data exposure, and implement practical, enforceable governance.
Prevention is better than a cure.
Arctic Wolf Aurora Endpoint Defense is a next generation end-point security solution for desktops and servers.
Aurora provides continuous threat prevention powered by Artificial Intelligence (AI).
Unlike traditional anti-virus products that rely on signatures to
detect
threats in the environment, Arctic Wolf Aurora Endpoint
Defense:
Aurora's EPP and EDR capabilities are unmatched and provide a Predictive Advantage of over 24 months (i.e., an end-user would have been protected even if they hadn’t updated their AI math model for over two years). Learn more
Protection against ransomware requires a multi-layered approach, with both preventative measures and recoverability capabilities. Learn how Hararei can provide complete protection at Ransomware Protection.
With unmatched effectiveness, minimal system impact, and zero-day prevention, Arctic Wolf Aurora protects endpoints and organizations from compromise.
Advanced threat monitoring, analytics, and expert human oversight to identify, investigate, and neutralize cyber threats around the clock.
The Managed Detection and Response (MDR) market is expanding rapidly as organizations seek smarter, faster ways to defend against an ever–evolving cyber threat landscape. With attacks growing in sophistication and an ever–increase shortage of skilled analysts, MDR has become the preferred approach for achieving continuous monitoring, proactive threat hunting, and rapid incident response.

Arctic Wolf’s MDR delivers round-the-clock monitoring, detection, and response across endpoints, networks, and cloud workloads. Leveraging advanced analytics and machine learning, the service surfaces and prioritizes threats in real time while a dedicated Concierge Security® Team works with your organization to guide containment, remediation, and long-term posture improvement. The result is a true security partnership that boosts visibility, accelerates response, and strengthens resilience against today’s rapidly evolving attacks.
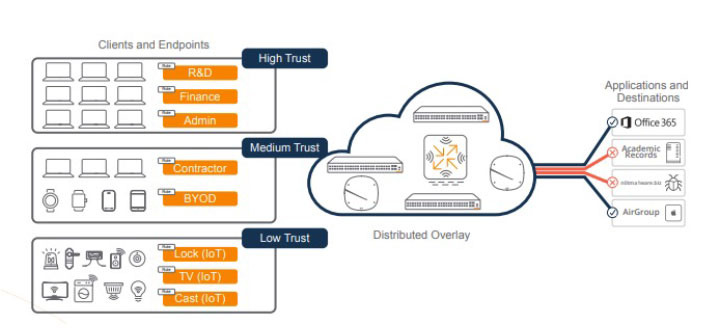
Most organisations have no reliable way to control who and what is connecting to their network. Corporate laptops, personal devices, IoT equipment, contractors, and guests often receive the same level of trust, increasing the risk of unauthorised access and lateral movement. Network Access Control provides the visibility and policy enforcement needed to ensure every device receives only the access it requires.
Network Access Control has become more important as organisations support a broader mix of users, devices, and locations. Corporate laptops, personal devices, contractors, guests, IoT systems, and unmanaged endpoints are all connecting to enterprise networks, often with different levels of trust and security posture.
Without effective NAC, organisations may struggle to identify what is connected, enforce consistent access policies, and limit lateral movement if a device is compromised. A modern NAC strategy helps ensure that users and devices are authenticated, authorised, profiled, and placed into the right level of access before they can reach sensitive systems.
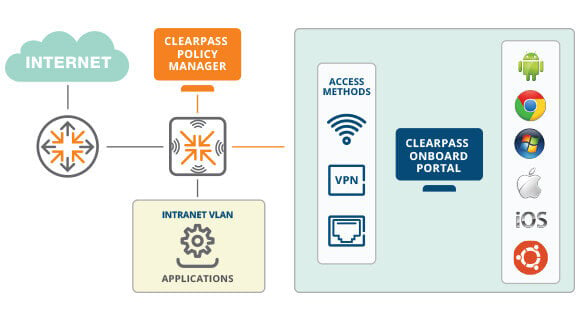
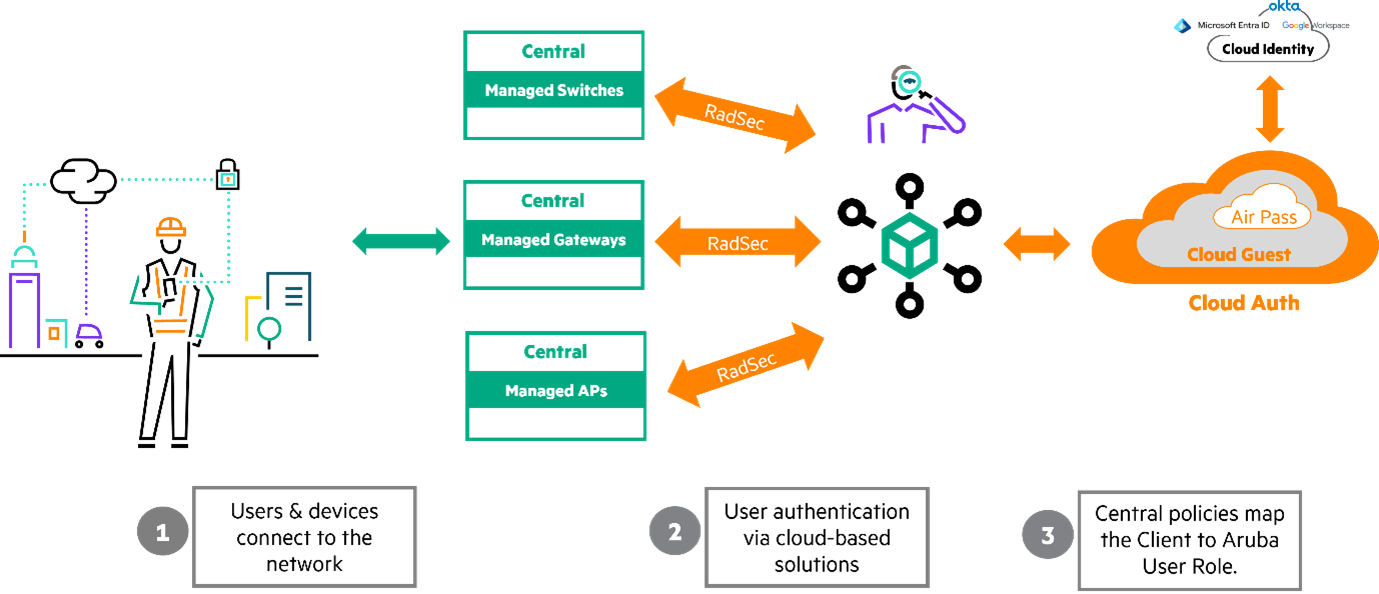
Aruba ClearPass provides a comprehensive NAC platform with capabilities that support access control, device visibility, posture assessment, BYOD onboarding, and guest access across wired, wireless, and remote network environments.
Central policy engine for authentication, authorisation, role-based access control, and enforcement across multi-vendor networks.
Endpoint posture assessment to validate device health, security controls, and compliance before granting network access.
BYOD onboarding and certificate provisioning to simplify secure access for employee-owned devices.
Device discovery and profiling to identify unmanaged, IoT, OT, and other non-traditional endpoints.
Aruba ClearPass provides device posture control to ensure endpoints meet defined security standards before network access is granted. Using its OnGuard capability, ClearPass evaluates device health during authentication by checking attributes such as operating system version, antivirus status, firewall configuration, and overall compliance with corporate policies. These checks can be applied across wired, wireless, and VPN connections. If a device fails validation, ClearPass can restrict access, place the device into a remediation network, or apply limited access policies until the issue is resolved. This approach prevents vulnerable or noncompliant endpoints from reaching sensitive resources while maintaining seamless connectivity for trusted devices.
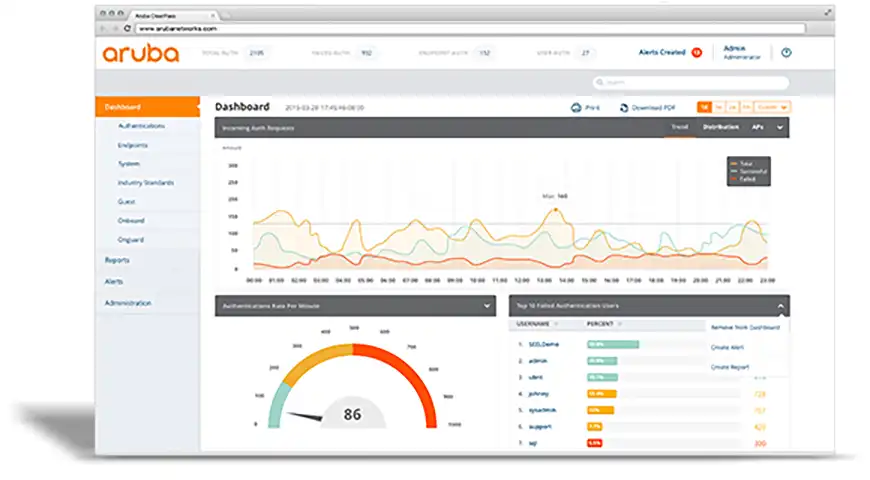
Aruba Networking ClearPass Policy Manager (CPPM) provides robust network access control with granular role-based policies for authentication, authorization, continuous monitoring and enforcement. Its highly interoperability feature helps customers to leverage their investment in earlier security products.
Aruba ClearPass gives you comprehensive and precise profiling, authentication and authorization for your users and guests, your systems, and devices trying to access your IT resources. It’s a rock–solid, affordable solution to control access to your network
HPE Aruba Networking ClearPass Policy Manager provides role and device–based secure network access control for Internet of Things (IoT), BYOD, corporate devices, as well as employees, contractors, and guests across any multivendor wired, wireless and VPN infrastructure.
With a built-in context-based policy engine, RADIUS, TACACS+, non-RADIUS enforcement using OnConnect, device profiling, posture assessment, onboarding, and guest access options, ClearPass is unrivaled as a foundation for network security for organizations of any size.
Enterprise networks are rarely built on a single vendor’s infrastructure. Aruba ClearPass is designed to operate across heterogeneous environments, integrating with multi-vendor switches, wireless networks, firewalls, and identity providers. By acting as a centralized policy engine, ClearPass enables organizations to enforce consistent authentication, device profiling, and access policies regardless of the underlying network hardware. This allows security teams to maintain uniform access control across existing infrastructure while avoiding costly rip-and-replace network upgrades.
With ClearPass, organizations can deploy wired or wireless using standards-based 802.1X enforcement for secure authentication. ClearPass also supports MAC address authentication for IoT and headless devices that may lack support for 802.1X. For wired environments where RADIUS based authentication cannot be deployed, OnConnect, offers an alternative using SNMP based enforcement.
HPE Aruba Networking ClearPass is the only policy platform that centrally enforces all aspects of enterprise-grade access security for any industry. Granular policy enforcement is based on a user’s role, device type and role, authentication method, UEM attributes, device health, traffic patterns, location, and time of day.
Hararei brings extensive experience designing and operating large-scale enterprise networks. We help organisations define access policies, integrate ClearPass with existing infrastructure, and develop a phased deployment strategy that delivers security improvements without disrupting business operations.
ClearPass Policy Manager Datasheet
While Zero Trust Network Access (ZTNA) has become a key component of modern security architectures, it addresses a different challenge than Network Access Control (NAC). ZTNA controls access to specific applications based on user identity, device posture and risk, whereas NAC controls which devices are permitted to connect to the network in the first place. NAC remains essential for securing campus and branch environments, onboarding new devices, enforcing network segmentation, and managing unmanaged assets such as printers, cameras, medical devices and industrial systems that cannot support ZTNA agents. Together, NAC and ZTNA provide complementary layers of protection, helping organisations implement a comprehensive Zero Trust strategy that secures both network connectivity and application access.
Network Access Control helps organisations demonstrate control over who can access sensitive systems and data. By enforcing authentication, device validation, role-based access policies, and continuous monitoring, NAC can support compliance initiatives across financial services, healthcare, government, and other regulated industries.
Hararei can assess your current network access controls, identify unmanaged devices, and help determine whether Aruba ClearPass is the right solution for your organisation.
Request a NAC Strategy Discussion
Patch management remains one of the most fundamental controls in maintaining a secure and reliable IT environment, yet it is also one of the areas where many organisations continue to struggle operationally. While most IT teams understand the importance of applying security updates promptly, the practical reality is often far more complex. Endpoints are no longer confined to a single office or corporate network, users operate remotely, and critical business applications now extend well beyond the operating system to include browsers, collaboration tools, document readers, and other third-party software. As a result, patching is no longer simply a matter of pushing Windows updates on a schedule. It requires continuous visibility into which devices are exposed, confidence that patches can be deployed regardless of location, and the ability to remediate vulnerabilities quickly without adding administrative overhead. When patching processes are inconsistent, delayed, or dependent on user behaviour, the result is not only greater security exposure, but also reduced operational control and more difficulty demonstrating compliance.
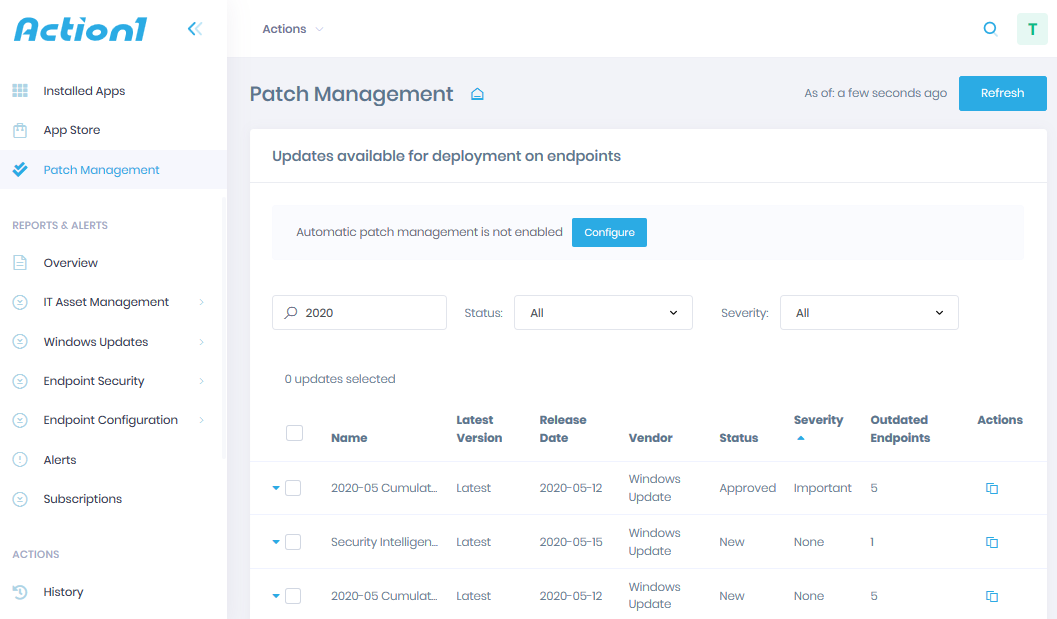
Hararei helps organisations address these challenges by implementing Action1 as part of a more practical and continuous approach to endpoint management. Action1 is a cloud-native platform that provides real-time visibility into patch status and vulnerabilities across endpoints, while allowing IT teams to deploy updates without relying on VPN connectivity or traditional on-premises infrastructure. By bringing operating system and third-party patching together into a single platform, it reduces the need for multiple tools and simplifies day-to-day operations. More importantly, it allows patching to move from a periodic administrative task to an ongoing operational control, where vulnerabilities can be identified and remediated as they emerge rather than waiting for scheduled maintenance windows. The result is a more consistent patching process, improved endpoint hygiene, and greater confidence that security exposures are being addressed in a timely and measurable way.
Many organisations already have patching tools in place, but still face practical gaps that increase both operational effort and risk. These challenges are typically not due to missing tools, but because those tools are not aligned to how endpoints operate today.
In distributed environments, these limitations can slow response to vulnerabilities and make compliance harder to demonstrate.
Action1 simplifies patching and endpoint control through a single cloud-based platform.
Understand exactly which endpoints are missing patches at any moment, without relying on delayed reporting.
Manage operating system updates and third-party application patching from a single console.
Patch and manage endpoints regardless of location, without requiring VPN connectivity.
Continuously identify and remediate missing patches to reduce exposure to known vulnerabilities.
Access and remediate endpoints directly without requiring separate remote support tools.
A modern patch management approach should do more than distribute updates. It should reduce the time between identifying a vulnerability and remediating it, improve coverage across all endpoints regardless of location, and provide clear, current visibility into patch compliance. In many organisations, patching remains a periodic task, often dependent on maintenance windows, user connectivity, and manual processes. This creates delays between exposure and remediation, increasing both risk and operational effort.
By contrast, a continuous and cloud-based approach allows IT teams to respond more quickly and with greater consistency. Action1 enables patches to be deployed as endpoints come online, without requiring VPN connectivity or user intervention. This removes a common point of friction in distributed environments and ensures that patching is no longer constrained by network boundaries or scheduled cycles.
From an operational perspective, this shift has a number of practical effects. IT teams spend less time tracking endpoint status, coordinating patch cycles, or following up with users to connect to the network. Visibility improves, as patch status and vulnerabilities can be viewed in real time rather than inferred from historical reports. Response times to critical vulnerabilities are reduced, allowing organisations to act more quickly when new exposures are identified.
Over time, these improvements contribute to a more predictable and controlled endpoint environment. Patch compliance becomes easier to demonstrate, audit preparation requires less manual effort, and the overall reliance on multiple overlapping tools is reduced. Rather than increasing complexity, patch management becomes a more integrated and manageable part of day-to-day IT operations.
Action1 is typically introduced where organisations have already invested in endpoint management or security tooling, but continue to experience operational gaps in patch coverage, visibility, or control. These gaps are often not immediately visible in reporting, but become clear when responding to critical vulnerabilities, supporting remote users, or preparing for audits.
In many environments, traditional tools remain dependent on network connectivity, scheduled update cycles, or multiple supporting systems to deliver a complete outcome. As endpoints become more distributed, these approaches can lead to inconsistent patching, delayed remediation, and increased administrative overhead.
Action1 fits into this environment as a lightweight, cloud-native control layer that simplifies how patching and remediation are executed. It does not require significant infrastructure changes and can be deployed alongside existing tools, allowing organisations to address specific operational gaps without committing to a full platform replacement.
It is particularly relevant in scenarios where organisations need to:
In these scenarios, Action1 provides a practical way to move from periodic patching processes to a more continuous and controlled approach to endpoint management, without introducing additional complexity.
Action1 is easy to try with a free trial, and for smaller environments the first 200 targets are free forever. Contact us for more details.
Governance, Risk, and Compliance is an integrated strategy that aligns IT, legal, finance, and operational departments to manage risks, meet regulatory requirements, and ensure company policies support business goals. It helps organizations avoid fragmented, inefficient, and costly operations silos
Automate certificate discovery, issuance, renewal, and revocation while maintaining visibility and control across your entire environment.
CertiNext simplifies digital certificate lifecycle management across cloud, hybrid, and distributed environments. It provides centralized visibility and automation to ensure certificates are properly issued, monitored, renewed, and governed—reducing operational overhead while maintaining security and compliance.
In complex environments, certificates are often managed across multiple teams and tools, creating gaps in visibility and consistency. CertiNext addresses this by continuously discovering certificates, enforcing standardized policies, and providing proactive alerts before issues arise. Integration with existing infrastructure and automation workflows ensures certificate management remains consistent and scalable.

Organizations today operate in an environment of increasing regulatory pressure, growing cyber risk, and expanding digital footprints. Governance, Risk, and Compliance (GRC) can no longer be managed through spreadsheets, disconnected tools, or periodic reviews. Quantarra provides a modern, SaaS-based platform that centralizes risk visibility, automates compliance processes, and enables organizations to demonstrate control in real time.
Most organizations approach GRC as a documentation exercise rather than an operational capability. Policies are defined but not enforced, risks are identified but not continuously monitored, and compliance efforts rely heavily on manual processes.
This results in limited visibility into actual risk exposure, inconsistent control enforcement, and significant effort during audits. As regulatory frameworks evolve and organizations adopt cloud and SaaS services, these gaps become more pronounced and more difficult to manage.
Quantarra brings governance, risk, and compliance into a single platform, allowing organizations to move from reactive reporting to continuous control and monitoring.
It enables organizations to define policies, map controls to regulatory frameworks, track risk in real time, and automate compliance workflows. By centralizing these functions, Quantarra reduces operational complexity while improving accuracy and accountability.
Quantarra provides a unified platform to manage governance, risk, and compliance as an ongoing operational function rather than a periodic exercise.
Gain a consolidated, real-time view of risk across systems, processes, and business units, enabling better awareness and faster decision-making.
Move from periodic audits to continuous compliance by mapping controls to frameworks and monitoring their effectiveness in real time.
Define, manage, and enforce policies and controls centrally, ensuring consistent governance across the organization.
Maintain complete audit trails and generate reports quickly, reducing effort and improving confidence during audits.
Align controls to multiple regulatory and industry frameworks, simplifying compliance across regions and requirements.
Automate compliance tasks, approvals, and remediation workflows to reduce manual effort and improve operational efficiency.
Collect, store, and manage compliance evidence in a centralized repository, ensuring traceability and audit readiness.
Access dashboards that provide up-to-date insights into risk posture, compliance status, and control effectiveness.
GRC platforms are only effective when aligned with real-world operational and regulatory experience. At Hararei, we help organizations implement Quantarra in a way that reflects their business processes, risk profile, and compliance obligations.
We bring experience across cybersecurity, cloud, and regulatory environments to ensure that GRC is integrated into the broader security and IT strategy, rather than operating as a standalone function.
Contact Us Please contact Hararei for an in-depth discussion on using any of our Cloud or Cybersecurity products or services