

Zscaler is a cloud-delivered security platform that extends Zero Trust protection to IoT and OT environments. While many OT systems have historically remained isolated for security reasons, this limits the ability to adopt Industry 4.0 initiatives such as real-time analytics, automation, and remote operations.
All your IoT/OT devices would essentially sit behind Zscaler's Zero Trust Exchange, so you can protect industrial control systems, SCADA systems, factory and manufacturing lines and other critical assets. Zscaler ensures these devices remain secure and compliant, minimizing downtime, attacks and data loss
The Zscaler platform leverages a global Cloud that runs at the edge of your devices for lightweight, fast connections which can scale much faster than any other IoT/OT secure access solution on the market.

Zscaler can help secure OT (Operational Technology) environments by providing a comprehensive security platform that can detect and prevent cyber threats before they reach the OT environment. Zscaler's cloud-based security architecture provides a secure and direct access to the Internet, eliminating the need for backhauling traffic through legacy security devices or appliances. It provided a single pane of glass to manage security across all locations, device and users, and enables seamless security operations.
Zscaler's zero-trust security model ensures that only authorized devices and users can connect to the OT network, reducing the attack surface and preventing unauthorized access. It can also help secure IoT devices and other OT assets, ensuring they are compliant with industry standards and regulations.
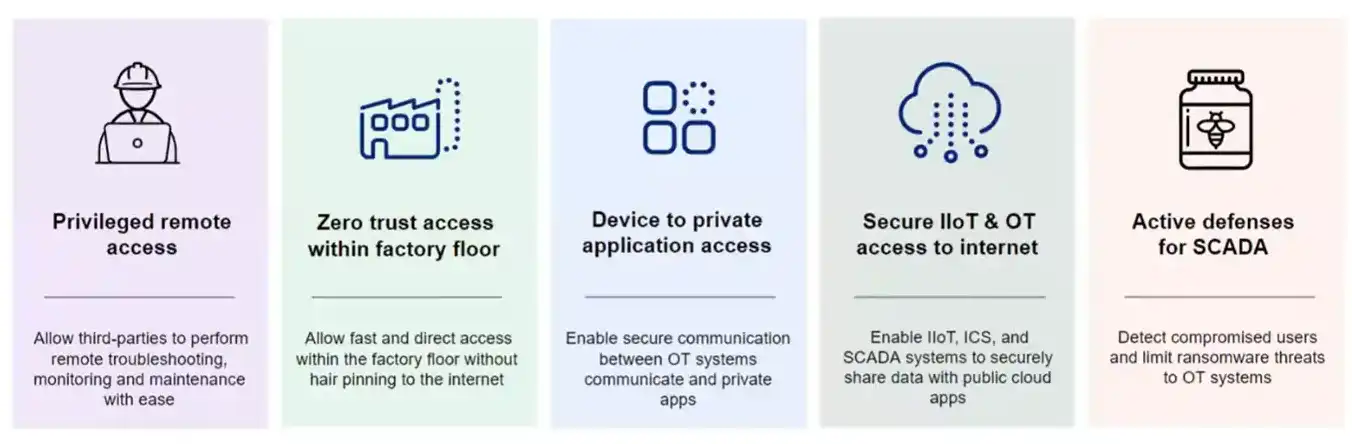
A zero trust approach is the most effective way to ensure robust ICS and OT security and achieve IEC 62443 compliance with adaptive, context-based application access that doesn’t depend on network access. With an effective zero trust architecture in place, any user can only access the applications and systems they need, with no complex firewall stacks or VPNs required, all while your apps and network stay invisible to the internet.
Zscaler solves IIoT and OT use cases by routing traffic through the Zscaler Zero Trust Exchange (ZTE). This solves for at least 5 differennt Use Cases
Modern manufacturing, logistics, healthcare, and critical infrastructure environments depend on the secure integration of operational technology (OT) and IoT devices with enterprise IT systems. However, these devices are often unmanaged, unpatchable, and inherently vulnerable. Bridging OT and IT without proper segmentation and inspection dramatically increases risk and expands the attack surface. A security-first architecture enables controlled connectivity, granular policy enforcement, and continuous visibility across all devices—allowing organizations to unlock real-time analytics, automation, predictive maintenance, and digital transformation initiatives without compromising safety or resilience.
From a technical standpoint, secure OT and IoT integration requires identity-aware segmentation, full traffic inspection, and policy enforcement independent of network location. Rather than relying on flat VLAN designs or perimeter firewalls, modern architectures apply zero trust principles to device communications—validating device identity, restricting east-west movement, and limiting access strictly to required applications and services. Continuous monitoring, encrypted DNS, and granular policy controls ensure that unmanaged or legacy devices cannot laterally propagate threats. This approach reduces blast radius, strengthens compliance, and provides the operational visibility required to safely scale connected environments.
From a financial perspective, securely integrating OT and IoT environments protects far more than data — it protects uptime, production capacity, and revenue. Unsegmented device networks increase the likelihood of operational disruption, regulatory penalties, and costly incident response. By enforcing granular segmentation and centralized policy control, organizations reduce the probability and impact of outages while lowering the long-term cost of managing fragmented security tools. A platform-based security architecture also simplifies operations, reduces vendor sprawl, and improves predictability of total cost of ownership, allowing Industry 4.0 initiatives to scale without introducing uncontrolled financial risk.
A zero trust approach is the most effective way to ensure robust OT security. With an effective zero trust architecture in place, any user—an employee, a contractor, or a third party—can only access the applications and systems they need to do their job, with no complex firewall stacks or VPNs required, all while your apps and network stay invisible to the open internet.
Hararei is a Cloud Generation solutions provider committed to helping clients prepare for, adopt and deploy the latest generation of applications, cybersecurity solutions and IT/Cloud infrastructure. Contact us today for a confidential discussion regarding all your Cloud and Edge requirements, including how to deploy Zero Trust in any environment.
Contact Us Please contact Hararei for an in-depth discussion on using any of our Cloud or Cybersecurity products or services